What is SSL?
SSL (Secure Sockets Layer) makes sure there’s a secure internet connection to protect data (think personal details and credit card information) being sent online. You can think of it like a private tunnel from your browser to the server receiving the information. The information is encrypted to make sure that no prying eyes can read or modify that information while it’s being transferred.
What is HTTPS?
Once your site is secured by a SSL certificate, HTTPS will appear in the URL. You’ll also get the coveted green padlock.

Google, who wants to ensure that users’ experience on the web is as useful and secure as possible, is encouraging sites to implement SSL in order to make sure the overall web is secure. In 2014, Google announced that they would give a ranking boost to encrypted sites.
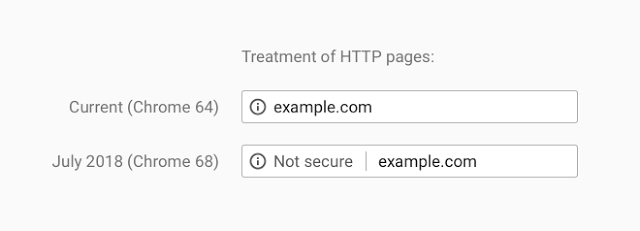
And, since July 2018, Google Chrome is pushing even further by marking non-https sites with a “Not secure” message in the browser bar.
At Strattic, we take security seriously. All sites on Strattic get a free AWS SSL certificate.
Why SSL is not enough
SSL is a necessary first step, but it’s not enough to fully secure your site.
Even if your site is SSL’ed, there are still vulnerabilities that are commonly exploited and there are steps that should be taken to help secure your site further.
Security headers to the rescue!
Whenever a browser requests a page from a web server, a server provides the browser with the content along with some useful information, called headers.
Many SSL-related vulnerabilities can be mitigated with a special type of headers, called security headers that can tell browsers how to treat content on a web page such as “whitelist certain types of content from trusted sites” or “only load this site over HTTPS”.
Security header #1: HTTP Strict Transport Security (HSTS) to solve man-in-the-middle attacks
When a site performs a 301 redirect from the http to the https version of a site, the redirect does not fully protect the site visitor, since it can be intercepted between when the visitor requests the http version of the site, and when it reaches the https destination, for a type of attack called a “man in the middle” attack.
In order to prevent this interception during a redirect, you can use the HTTP Strict Transport Security (HSTS) header, which allows site owners to instruct browsers to always go straight to the https version. This removes the window for the man-in-the-middle attacker since the http version of the site is never accessed, not even for a second.
In order for sites to be HSTS-enabled, the HSTS header “Strict-Transport-Security” must be in place, the site must meet a number of criteria outlined here, and then be submitted to the HSTS Preload list.
Because security is extremely important to us, we have implemented HSTS for all our client’s websites. In order to complete the process, all our clients have to do is fill out the HSTS Preload form to get added to it. You can read more about HSTS and possible drawbacks here.
Security header #2 Content Security Policy (CSP) to solve mixed content errors
A Content Security Policy (CSP) uses browsers to detect and mitigate certain types of attacks like cross-site scripting (XSS), clickjacking and other code injection attacks resulting from execution of malicious content in the trusted web page context. A CSP can be used for simple purposes like enforcing HTTPS on SSL-enabled sites, to more sophisticated uses like authorizing only truly trusted sources and blocking others.
Using CSP also makes sure that there are no mixed content errors on your site. For example, if your site is on https but you embedded a YouTube video with a http link, then you would otherwise wind up with mixed content errors in the browser console. These mixed content errors will prevent the green padlock from displaying next to your url in the browser bar. A CSP could direct a website to make make all urls are always https, to avoid any mixed content errors.
To learn more about CSP, watch Miriam Schwab, CEO of Strattic’s presentation at WordCamp Europe.
Most sites do not have a CSP installed, but it’s important to be aware of it and how it can be used to add an additional layer of security to your website.
All Strattic sites come with an automated and customized CSP.
Conclusion

Most site owners think that once they’ve added a SSL certificate to their website, they can move on and go drink a piña colada on the beach. That would be nice if the web was all rainbows and unicorns. But as we’ve seen, the web has plenty of hackers trying to ruin..well, just about everything. So, to harden your site’s SSL, make sure to implement HTTP security headers such as HSTS and CSP. Or, you can give Strattic a try, and we’ll take care of it for you.



