Reports show that WordPress is the most hacked platform on the web. But that doesn’t mean your site has to be hacked too. In fact, keeping WordPress safe is pretty easy. After a decade of hosting and maintaining WordPress sites at illuminea, many of which are highly targeted by hackers and have even been shared on the dark web, we’ve had to learn how to keep them secure without going crazy. We’ve found that there are a few simple measures that site owners can take that cover 90% of the security issues. We’ll also look at tools and tweaks that can harden and protect your sites even more. Most of these steps can be implemented by beginner users, while some need more experience.
That’s why I decided to give a talk “WordPress Security for All – You Won’t Believe How Simple It Can Be” at WordCamp Europe 2017 in Paris.
Make sure to read to the end to see how a revolutionary approach to website security is starting to gain momentum.
Level 1 Security: At the very least
1. Update! Update! Update!
This one’s obvious – make sure you update ALL plugins, ALL themes, and ALL WordPress core updates. Even if it breaks something. Just do it! This is probably the number one reason sites get hacked – out of date WordPress plugins and installations. If you think you’ll forget, you can add some lines of code to wp-config file or use an automatic update plugin or if you manage multiple sites, you can use Jetpack (free), ManageWP or InfiniteWP.
2. Backup!

Do you have a daily backup that you know is 100% reliable and can be restored in a few minutes? If not, you really, really, really should. We happen to love blogVault for their reliable off-site backups, easy restores, test-restores, and migration features. They also have an amazing malware scanner that alerts you if any of your sites are infected. So if your site gets hacked, you can clean the malware or go back and test-restore previous backups to see which version wasn’t infected.
3. No “admin” username
Obvious, but just know that you should never have an admin username. Create a new user and delete the default admin username and move any posts to the new username.
4. Limit login attempts

You can set how many times people can try to login to the Dashboard. This is the main cause of brute-force hacks which is people trying to login unnaturally too many times.
These tools can help you limit the number of login attempts:
5. Strong passwords
Please don’t use real words or “ilovemydog”. Use a password generator. Be wary of password managers. Best to use a pattern for each site.
6. Reliable hosting provider
Don’t go with cheapie shared hosting. You’ll need high level, responsive support who can easily clean or restore your site if something happens to it.
Level 2 Security: Rockstar level
7. Minimum number of admin users
Make your user permissions as low as possible, and delete or demote any unused users. User permissions should be based on what they need to access in the Dashboard. Every admin user is a potential gateway into your site.
8. Delete unused plugins
Every once in a while, do an audit of your site and see what’s running that you don’t need. Be ruthless, delete whatever you don’t need.
9. Only use reliable plugins
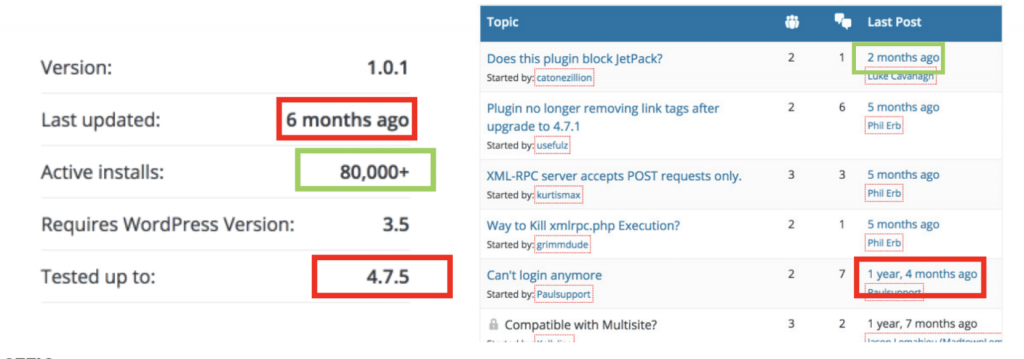
The WordPress plugin repository has some helpful data you can access about every plugin. A plugin should ideally be tested with the latest version of WordPress and be updated within the last six months or so. Look at the support section to see if the developer is actively engaged in the plugin.
10. 2-factor authentication

I’d recommend using 2-factor authentication on pretty much everything including gmail, Facebook, and your website. You can use Wordfence or Jetpack.
Level 3 Security: outta sight
11. HTTPS
Every site should have SSL. And with HTTP/2 it actually runs really fast, not like in the olden days. Google wants your users to feel secure, and you should too. Aside from the security benefit, Google has added SSL as a ranking factor so if you want to give your site a little push, you should make your site SSL. This is really important.
12. SFTP
Don’t use regular FTP when connecting to your server.
13. Don’t allow file editing in the Dashboard
Don’t allow theme or plugin file editing from the Dashboard. If someone gets access to your Dashboard, you don’t want them to be able to access your files.
You can add this to your wp-config file:
define(‘DISALLOW_FILE_EDIT’, true);
14. Firewalls
Firewalls are really important for blocking a malicious request before it connects to your database and before WordPress code loads. You can use WordFence for this
15. Update to latest PHP version
It’s really important to update to the latest PHP version since older versions are no longer supported and could be a major vulnerability.
16. Check file permissions on the server
You can check default file permissions in the Codex.
17. Database prefixes
This is a debate in the WP community. If you use the default WP database prefix, does that make your site more vulnerable? My opinion is that if you’re going to do it, do it when you first install WordPress. But if you’ve already got it up and running, you can leave it. We’ve found this not to be a serious security vulnerability.
18. Keep your own computer clean
Make sure your computer is clean so that you don’t accidentally infect your sites.
19. CDN
You can try to use a CDN to protect against DDoS attacks. And it can also help speed up your site.
20. Remove WP version
Meh. Hackers can still identify your site as WordPress, so… it’s not really necessary.
21. Create WP security keys and salts and put them in wp-config
Phew. That was a lot. This is all stuff we should all do. If you do level one, you’re in pretty good shape. And if you have backups, even if something happens, you have something to go back to.
Keep an eye on your site
Here are some tools to help you scan or monitor your site so you’re the first to know if something goes wrong.
- Sucuri
- Wordfence
- Google Search Console Google wants the web to be a clean place, so as soon as they identify something, they send you a notification immediately.
- Jetpack Downtime monitor tool is very accurate. And free. It’ll send you a notification of something going wrong with your site or server immediately. It also tells you how long the site was down.
- Blogvault Malcare service
Level 4 security: Completely rethinking website security
Over our many years of running a WordPress agency, we’ve suffered from many security issues and we spent way too much time trying to fix security issues and fighting DDoS attacks instead of working on website development.
Then I started learning about AWS Lambda and serverless and realized that this is going to be the future of hosting and web development.
It’s called serverless because instead of running a dynamic server all the time to process some kind of dynamic functionality, it’s essentially static sites but the dynamic functionality runs on demand and then shuts down.
The benefit of going serverless is that there’s no database and there’s no dynamic server running so all the attack surface and vulnerabilities are actually eliminated and sites run faster because they don’t have to do database queries for every page. And they’re more scalable.
And most importantly, I wanted to keep using WordPress, a dynamic system, for managing our content since it’s great for generating leads, traffic, and business.
So, how do we marry the awesome worlds of WordPress and serverless?
Enter… Strattic!
How it works
Strattic disconnects the dynamic WordPress site from the web and puts it on a different url behind authentication so only site owners can access that site. You can continue using your WordPress like you always have – marketing people can still add content, you can still add plugins, and so on.
Then you deploy your site with one click of a button. Your changes get deployed as HTML, CSS and Javascript, essentially the front-end of your site without the underlying vulnerabilities. Site visitors are visiting an exact clone of your WordPress sites. But without the vulnerabilities – bots can’t hack the site because there’s no database there. Buhbye bots.
As a happy byproduct, the sites are also faster and scale even when hit by a lot of traffic or DDoS attacks.
We’d love to hear your feedback!




